NEW Closing the Gap Background
About the Closing the Gap Initiative
Navigate to:
Closing the Gap Home Page | Background | Conference Agenda | Resources | Advisory Board | Continue the Conversation
Closing the Gap: A DoD Conference on Re-entry for Women Veterans into Cybersecurity Careers addresses two crucial needs: To fill the exponentially growing cybersecurity talent gap in the U.S., and to harness the potential of female U.S. veterans to fill the gap.
Please review details on the conference here.
Background
In order for the United States to remain a world leader in various fields of science and technology, we need a robust and educated cyber-workforce. The Center for Strategic and International Studies (CSIS.org, January 2019) noted that “A recent CSIS survey of IT decision makers across eight countries found that 82 percent of employers report a shortage of cybersecurity skills, and 71 percent believe this talent gap causes direct and measurable damage to their organizations. According to CyberSeek, an initiative funded by the National Initiative for Cybersecurity Education (NICE), the United States faced a shortfall of almost 314,000 cybersecurity professionals as of January 2019. To put this in context, the country’s total employed cybersecurity workforce is just 716,000. According to data derived from job postings, the number of unfilled cybersecurity jobs has grown by more than 50 percent since 2015. By 2022, the global cybersecurity workforce shortage has been projected to reach upwards of 1.8 million unfilled positions.”
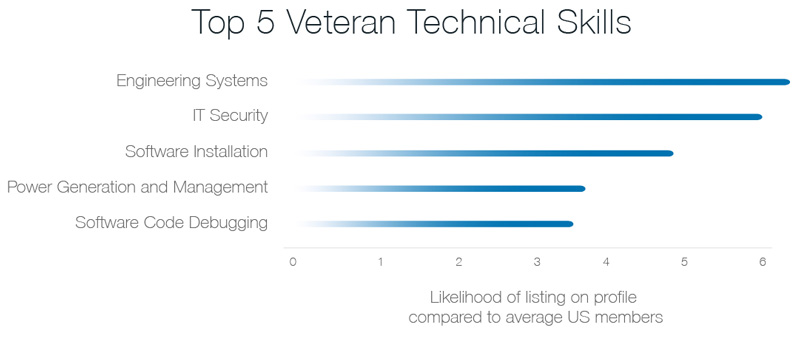
Women veterans are well positioned to fill this gap.
“Closing the Gap” refers to either a talent gap of skilled cybersecurity workers or a gap in the time between jobs in the military and the cyber-workforce. Closing the Gap is a working conference combining presentations and discussions focusing on the research in cyber workforce development and gender issues. By bringing together a variety of stakeholders in this topic, the conference will address how to overcome challenges in recruitment, representation and retention of women veterans in the cybersecurity workforce.
Being available to enter the workforce is not the same as being ready or equipped with the understanding of issues, challenges, barriers or strategies to re-entry, and in fact surveys by the Student Veterans Organization (SVA) report veterans pursuing and reporting interest in pursuing degrees in science, technology, engineering, math and medicine (STEMM) degrees is higher than the rate of those graduating. There are therefore opportunities before and during transition from the military, during recruitment and enrollement in college, and during college, to impact the choices of women veterans and bring them to opportunities in cybersecurity.
Leveraging Prior Knowledge to Enable Entry to Cybersecurity Fields
A problem in reentry is often that the vocabulary of the two groups (those seeking reentry and those offering education or employment) may not be on the same wavelength. The groups often use different terms for the same or similar issues, but neither group appreciates the other’s information. Whether a woman is seeking to complete a degree or move into the workforce, the focus of this session is establishing and/or assembling re-entry programs, courses and experiences, as well as ways to adapt or adopt them to return to education options or to the workforce. The education being sought could range from a few refresher courses, to a certificate, to an undergraduate or graduate degree. The key questions to be addressed include:
- Academic credit: How does one gain academic credit for any prior education or experiences?
- Prior Experience: How does one highlight and present prior experiences in terms of workforce skill sets?
- Skills: How does a woman who has taken a break from her career keep her tech skills up to date while in the Gap?
Moving from a Military to Non-Military Environment
We will review challenges facing women veterans. Many have been in the service for years; 10 or 20 years is not unusual. Conversely, a significant number of young women veterans choose to leave the military after just a few years. Many female veterans are dealing with the challenge of PTSD, and some specifically with Military Sexual Trauma (MST). Just as in non-military environments (perhaps more so), women face discrimination, gender inequalities, and harrassment.
In some cases, women may not have been welcomed back to society as "true veterans" in the same way as their male veteran colleagues. As they attempt to transition, they are learning new accepted social and work norms at the same time as they may be dealing with issues of survival. For those who are facing difficulties determining a path forward, or even the next step forward, we seek to support their journeys in overcoming the challenges in order to consider entering cybersecurity careers.
This topic is complex and compounded, and we attempt to bring together a diversity of perspectives to address it holistically as we focus on best practices for a successful transition. Key questions to be addressed in brainstorming sessions include:
- Two worlds: How is the non-military environment different from a military environment?
- Transitions:
- Military to non-military: What are the available resources to make the move from a military career to a non-military environment?
- Transition to cybersecurity: How do women service members make successful transitions to a cybersecurity workforce or career?
- Aiming for success: What are examples of a successful transition? What does it look like?
- Preparing women veterans
- Ways to prepare: What are some of the ways in which woman vets can prepare themselves?
- Job descriptions: How do military operating specialties (MOS) translate into civilian job descriptions?
- Resumes: How do women service members translate their military experiences into viable content for resumes for cybersecurity positions in the civilian sector?
- Supporting women
- Issues of gender and sexism in the workplace: What resources can women turn to for help?
- Mentoring: What are successful mentoring and networking practices to support women succeeding in cybersecurity workforce positions?
- Advancement: What structural barriers are women faced with in advancing their careers? What are best practices for advancing women through the “pipeline” toward a cybersecurity-focused position?
- Unconscious bias training: What aspects of unconscious bias training can (or should) be provided for educators, supervisors and career employment officers?
- Academics: What are the appropriate academic programs available?
White Collar, Blue Collar, New Collar: New Work Paradigms
The conference will address the changing landscape of the jobs available in the cybersecurity workforce, the backgrounds needed and the current trend in upskilling or improving workers’ IT skills.
Definitions
- White Collar: A typical Bachelor's degree in cybersecurity, computer science, information assurance, programming, etc. route to a technical position
- Blue Collar: Technical training for cybersecurity equipment repair and facilities security
- New Collar: Preparation for 21st century workforce of online jobs; retraining from one field to another; returnships and internships for adults. This is particularly important for women who have been in a gap from work or school. Cybersecurity and related technology fields change rapidly, and upskilling or apprenticeships might be the remediation needed.
NIST NICE Cybersecurity Workforce Framework
We will look at workforce job descriptions and a framework to match skills to job, such as the NIST/NICE “Cybersecurity Workforce Framework” 800-181. To the veteran looking to enter the field, this framework can be a major convenience as military duty assignments in information technology and assurance may not have defined the skill sets now being recognized as important academic elements for preparation. Job titles and responsibilities can help identify skill gaps in ways that the veteran feels comfortable. Closing the Gap will create the beginning of a list that will enable a veteran to self assess and identify gaps needed to address in order to prepare for a cybersecurity job and for college admission or corporate leaders to match the veteran’s skills with the requirements.
Key questions to be addressed:
- Returnships: How does a company successfully establish a returnship?
- New skill training paths: What does the experience of gaining new skills entail? How can you use current knowledge to strengthen and broaden your skill base?
- Alternatives to academic training: Are there new strategies to present an individual’s skills and capabilities in cybersecurity to a recruiter, other than the traditional “Bachelor’s Degree” requirement?
- The hiring perspective: How can a company utilize women’s overall experiences to fully take advantage of their skill sets, while also helping them develop new skill bases?
Interested in Joining the Conversation?
The Closing the Gap Conference planned for May 25 will be an interactive conversation amongst industry, academia, military and intermediary organization representatives, as well as women veterans. To gain entry, please submit your application below.
Continue the Conversation

